Getting Started
We built the Spectral platform from the ground up to have fantastic developer experience (DX). Spectral Scan is a single self-contained binary, that's easy to get and use.
Your first scan
After you've signed up, grab your SPECTRAL_DSN and run one of the following.
Universal installer for mac/Linux:
Or for Windows PowerShell:
All of the above are great. Pick the one you like 🤘
Make your first scan:
tip
As a security best-practice, you should never run curl | sh blindly. Feel free to inspect our install script (it's a shell script) before running.
Your first match
Assuming you're still in spectral-test, let's create a dummy secret:
We see our match. We have our file, a location (0:20), severity (Error), description and detector code (CLD001).
Spectral is secure by default
We never dump the actual secret or key to the console, or anywhere. If you want to see it, add a SPECTRAL_SHOW_MATCH=1 environment flag before running.
Kicking the tires 💥
To get an idea of the amount of stacks Spectral can analyze, you can use our codesec-goat repo.
What's a "goat" project?
A common saying is that if your fence won't hold water, it won't hold a goat. Animals are very creative, and will find a way around your barriers. In the same funny analogy, a goat repo demonstrates creativity and deliberate security issues that you might not expect.
Assuming you unzipped codesec-goat somewhere, let's run Spectral scan:
You'll see a wealth of findings ranging around the following topics:
- Sensitive data
- Credentials and access controls
- Misconfiguration
- Tech stack bad practices
Our idea is: we build an understanding of everything that can lead to security minded human errors, and poses a high risk. Then we look for it, detect it, and help you block and mitigate it.
Make it stick
Now that you've seen what Spectral can do, you can plug it into your development processes so that you're safe all the time. Like any new process for a dev team, we need to make the process stick.
One of the most recommended places to integrate Spectral to is your CI.
Never hold up a build
We build Spectral for performance. Every day. That's actually a business KPI of ours. Spectral scans an average sized repo in a second. Thanks to Rust and our low-level engineers, we're very happy.
Let's see how Spectral works in CircleCI (we support every popular CI there is today):
Before
Now you need to add your SPECTRAL_DSN to CircleCI (look here for how to do that). And use this configuration:
tip
As a security best-practice, you should never run curl | sh blindly. Feel free to inspect our install script (it's a shell script) before running or store it in your repo for safekeeping.
Data privacy: never see, never store policy
Spectral never sees your code or data, it never leaves your data center, and we never store any of your private code or data. We do this by packing all of our technology inside Spectral scan, so we don't need a backend.
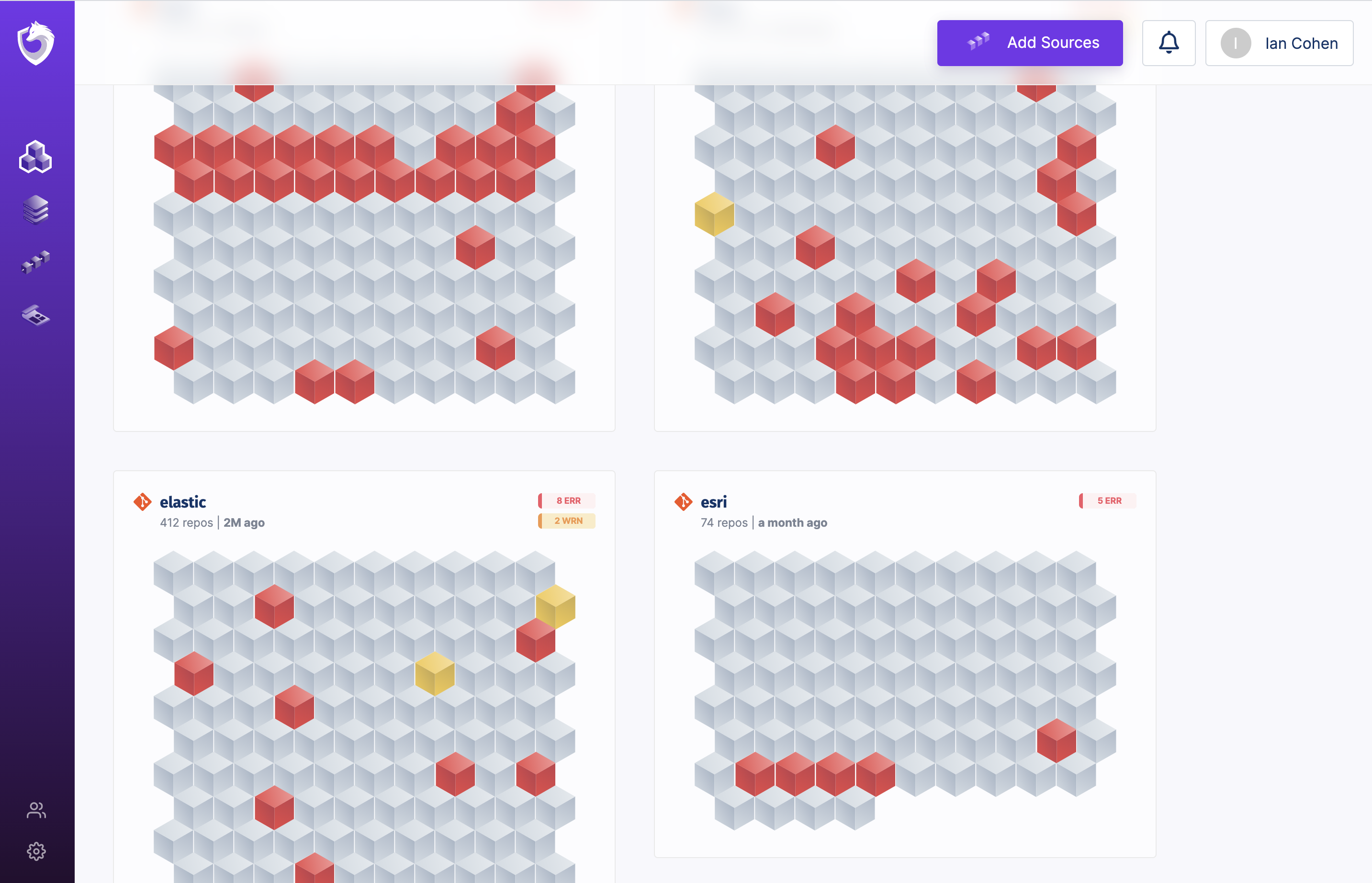
Our scanner sends back only metadata (file names, match location, primarily) so that we can show you where your problems are in our SaaS.
Now, you should both have nice reporting in your CI and in your Spectral account: